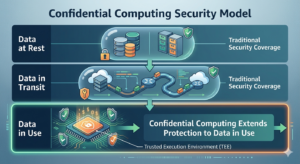
For decades, cybersecurity strategies have focused on protecting data at rest and in transit. Encryption standards, identity controls, and network defenses have matured significantly. Yet one critical gap has remained: protecting data while it is being processed.
As organizations increasingly adopt cloud computing, AI-driven analytics, and distributed architectures, sensitive data often leaves traditional security perimeters. Financial records, healthcare data, intellectual property, and personally identifiable information (PII) are processed in shared environments where traditional safeguards cannot fully mitigate insider threats, memory scraping, or compromised operating systems.
This is where confidential computing emerges as a transformative paradigm. By leveraging hardware-based Trusted Execution Environments (TEEs), confidential computing ensures that data remains encrypted not only at rest and in transit but also in use. Secure enclaves’ isolate computation from the host system itself, creating verifiable trust boundaries even in untrusted infrastructures.
Global technology leaders and standards bodies recognize its significance. Analyst reports indicate that confidential computing adoption is accelerating across industries handling regulated or high-value data, including banking, healthcare, government, and AI research.
In an era defined by data collaboration, cloud sovereignty requirements, and advanced cyber threats, confidential computing is no longer experimental, it is rapidly becoming foundational to secure digital transformation.
Table of Contents
ToggleIndustry Overview & Key Concepts
Confidential computing is emerging as a critical approach in modern cybersecurity, especially as organizations handle increasingly sensitive data across distributed environments. Understanding its foundational concepts is essential to grasp how it enhances data protection during processing.
What Is Confidential Computing?
To begin with, it is important to understand what makes confidential computing different from traditional security approaches. Unlike conventional methods that protect data only at rest or in transit, confidential computing focuses on securing data even while it is being processed.
Confidential computing is a security approach that protects data during processing by isolating workloads within hardware-based secure enclaves. These enclaves operate inside a Trusted Execution Environment (TEE), preventing unauthorized access from the operating system, hypervisor, or even privileged administrators.
Key capabilities include:
Encryption of data in memory
Isolation of application execution
Protection against insider threats
Secure multi-party computation
Remote attestation for trust verification
Trusted Execution Environments (TEEs)
At the core of confidential computing lies the concept of Trusted Execution Environments. These environments provide the foundational layer that ensures secure and isolated execution of sensitive workloads.
A TEE is a secure area within a processor that ensures code and data loaded inside it are protected in terms of both confidentiality and integrity. It acts as a shielded space where sensitive operations can run without exposure to external interference.
Common characteristics include:
Hardware-enforced isolation
Secure boot and runtime protection
Cryptographic verification
Resistance to tampering
Minimal attack surface
Secure Enclaves
Building on TEEs, secure enclaves serve as the actual execution units where sensitive computations take place. They are designed to ensure that even highly privileged system components cannot access or manipulate the data being processed.
Secure enclaves are the operational units within TEEs where sensitive computation occurs. Applications running inside these enclaves cannot be inspected or altered by external software components, ensuring a high level of trust and security.
Common use cases include:
Processing encrypted financial transactions
Privacy-preserving machine learning
Secure data sharing across organizations
Digital identity verification
Blockchain-based confidential smart contracts
Core Framework, Methodology, or Process
Implementing confidential computing requires coordinated efforts across hardware, software, cloud platforms, and governance frameworks.
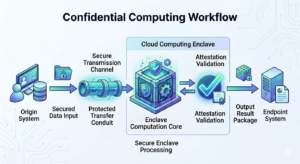
Trust Establishment Through Hardware Roots
Security begins with hardware-level trust. Modern processors include embedded security modules that verify firmware integrity during boot. This ensures that the environment hosting enclaves is not compromised from the start.
Secure Enclave Creation
Applications are partitioned so sensitive components run inside enclaves while non-sensitive logic operates normally. This minimizes performance overhead while maximizing protection.
Remote Attestation
Before data is shared with an enclave, external systems can verify that the enclave is genuine and running approved code. This process establishes trust across distributed environments.
Encrypted Data Processing
Data remains encrypted until it enters the enclave. Inside, it is decrypted only within protected memory, processed securely, and re-encrypted before leaving.
Policy Enforcement & Monitoring
Access policies, logging, and runtime monitoring ensure compliance with regulatory and operational requirements.
Key Challenges Organizations Face
While confidential computing strengthens data security, its adoption comes with a set of practical challenges that organizations must address.
Integration Complexity
Most legacy systems are not built for enclave-based execution. This makes it necessary to refactor applications to isolate sensitive workloads and adapt them to secure memory environments, which can be resource intensive.
Performance Overhead
Despite ongoing optimizations, TEEs can introduce latency due to encryption and isolation layers. This impact is more noticeable in data-heavy workloads, requiring careful performance planning.
Limited Developer Expertise
As an emerging field, confidential computing faces a shortage of skilled professionals. Limited familiarity with enclave programming models can slow implementation and increase reliance on specialized expertise.
Tooling and Ecosystem Maturity
The supporting ecosystem is still evolving. Compared to traditional cloud tools, debugging, monitoring, and orchestration capabilities for enclave workloads are less mature, which can affect operational efficiency.
Regulatory and Compliance Alignment
Organizations must ensure that implementations align with industry regulations, such as financial and healthcare standards, adding another layer of complexity to adoption.
Best Practices and Implementation Strategies
A structured approach helps organizations adopt confidential computing effectively while minimizing risks.
Identify High-Value Use Cases
Prioritize workloads involving sensitive data, such as financial transactions, healthcare analytics, intellectual property, cross-border data sharing, and AI training on private datasets. This ensures maximum value from implementation.
Adopt a Zero Trust Architecture
Confidential computing complements Zero Trust by securing data even during processing, reducing dependency on trusted infrastructure.
Use Hybrid Security Models
A layered security approach, combining TEEs with encryption, identity management, and network security ensures comprehensive protection.
Implement Strong Key Management
Managing the full lifecycle of encryption keys is critical to maintaining data confidentiality and preventing unauthorized access.
Start with Pilot Deployments
Begin with smaller, controlled deployments to validate feasibility and address challenges before scaling across the organization.
Future Trends and Industry Evolution
Confidential computing is set to play a key role in shaping secure digital ecosystems.
Privacy-Preserving AI
TEEs enable secure AI training on sensitive datasets without exposing raw data, supporting responsible and ethical AI development.
Multi-Party Data Collaboration
Organizations can collaborate and analyze shared data securely without revealing proprietary information, unlocking new business opportunities.
Secure Edge Computing
As IoT and edge technologies grow, confidential computing will help protect data generated outside centralized cloud environments.
Sovereign Cloud Initiatives
With increasing focus on data sovereignty, confidential computing ensures sensitive data remains protected even in global cloud infrastructures.
Integration with Blockchain
Combining confidential computing with blockchain enables secure smart contracts and confidential digital transactions, enhancing trust in decentralized systems.
How Round The Clock Technologies Delivers Confidential Computing Solutions
Round The Clock Technologies enables organizations to adopt confidential computing through a comprehensive, engineering-led approach that aligns security innovation with business outcomes.
Strategic Consulting Approach
The engagement begins with a detailed assessment of data sensitivity, regulatory requirements, and risk exposure. Security architects identify high-impact use cases where confidential computing delivers maximum value.
Implementation Methodology
Our team follows a phased deployment model:
Security architecture design
Pilot enclave deployment
Application refactoring and integration
Performance optimization
Enterprise-scale rollout
Technology Expertise
The engineering teams possess deep expertise in:
Trusted Execution Environments
Cloud-native security architectures
Zero Trust frameworks
Secure data pipelines
Privacy-preserving analytics
Engineering Capabilities
Our data engineering team designs and builds secure systems that integrate seamlessly with existing enterprise infrastructure, minimizing disruption while enhancing protection.
Tools, Platforms, and Frameworks
Solutions leverage leading hardware and cloud platforms supporting confidential computing, along with advanced encryption, identity management, and monitoring tools.
Industry Experience and Domain Knowledge
With experience across finance, healthcare, technology, and government sectors, RTC Tek understands the unique compliance and operational requirements of regulated environments.
Enabling Scalability, Performance, and Transformation
By combining secure enclave technology with cloud-native engineering practices, Round The Clock Technologies helps organizations:
Protect sensitive data across distributed systems
Enable secure collaboration and analytics
Accelerate digital transformation initiatives
Maintain performance and operational resilience
Confidential computing is not just a security enhancement; it is a strategic enabler of trusted innovation. Our holistic approach ensures organizations can adopt it confidently, efficiently, and at scale.